Investment
Forbes
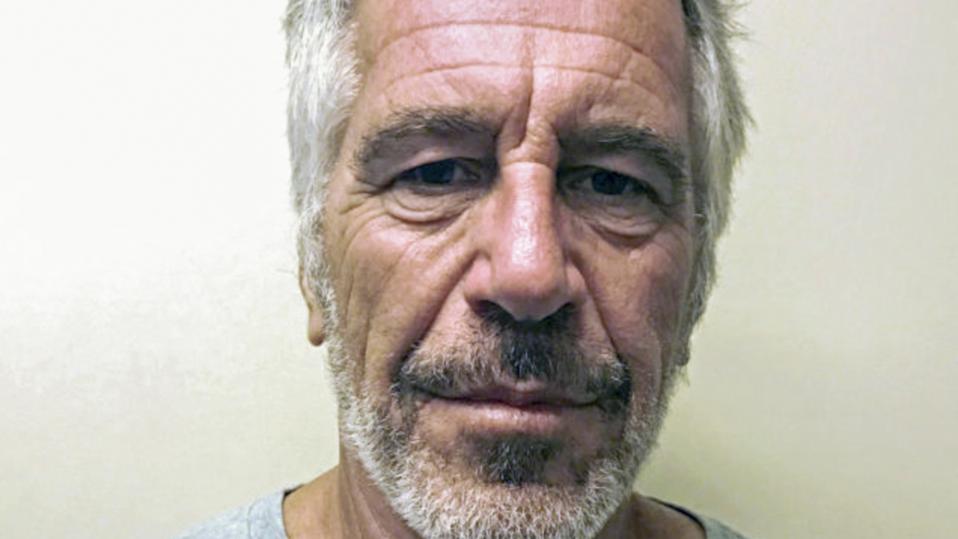
‘Missing’ Epstein Video—Digital Forensics Experts Reveal What Really Happened
Why This Matters
Missing Epstein Video—Former FBI Examiners reveal what really happened. Here's what you need to know.
July 27, 2025
01:19 PM
9 min read
AI Enhanced
Positive
FinancialBooklet Analysis
AI-powered insights based on this specific article
Key Insights
- Financial sector news can impact lending conditions and capital availability for businesses
Questions to Consider
- Could this financial sector news affect lending conditions and capital availability?
Stay Ahead of the Market
Get weekly insights into market shifts, investment opportunities, and financial analysis delivered to your inbox.
No spam, unsubscribe anytime